Table of contents
Most people do not realize, that anyone driving down the street could be gathering information about your network. It is a process, called wardriving. GPS data and Wi-Fi monitoring becomes paired. All that needs to happen is a mode of transportation to map the two together.
The term “wardriving” originated from “wardialing,” used in the popular classic film, WarGames. Same exact principle applies. But it is done using physical transportation methods to acquire information.

In the most literal sense, location data is linked with your wireless network. That means vulnerabilities risk being exposed. The cyber criminals only need to drive by your house to identify those weaknesses.
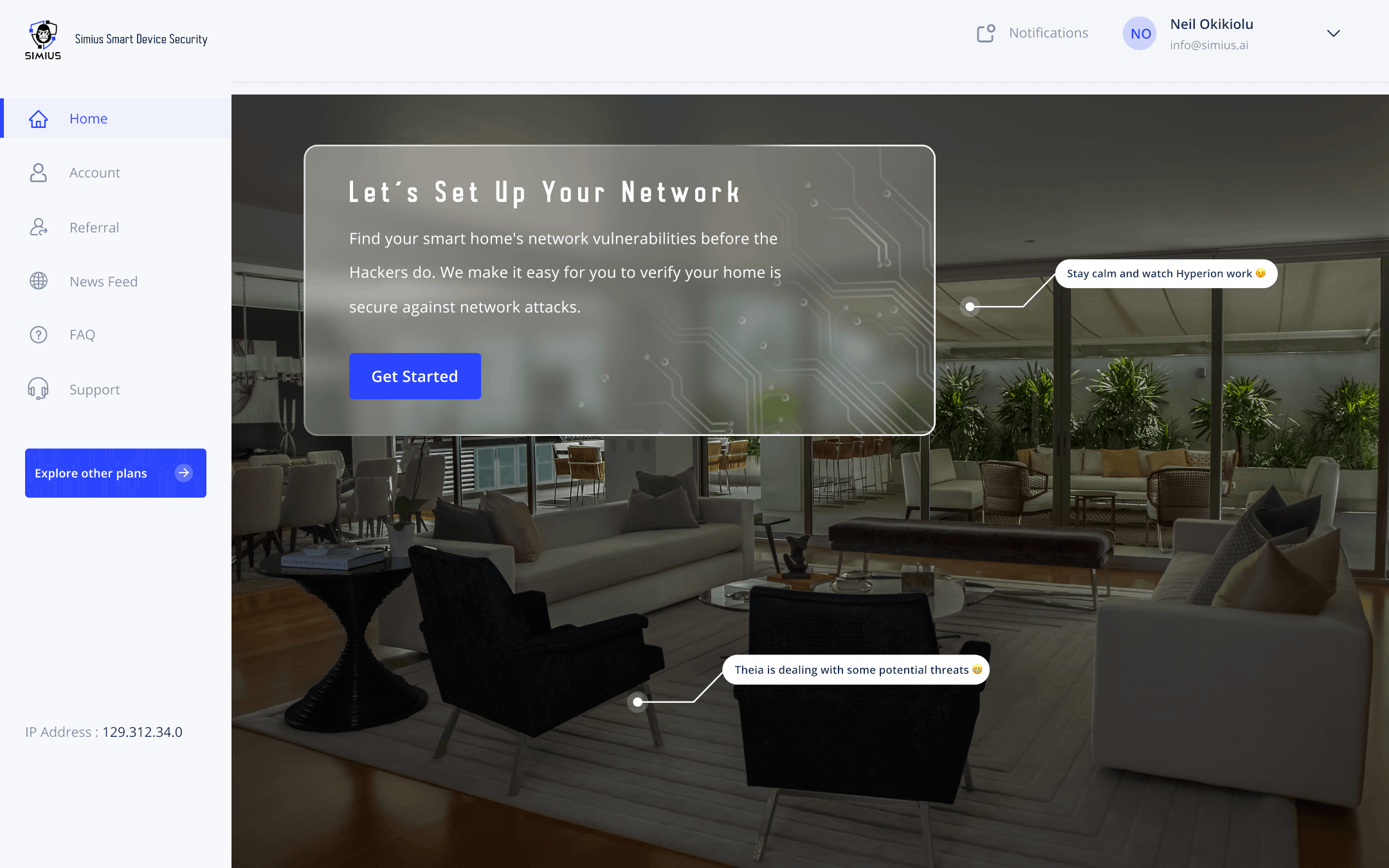
As they travel in vehicles over a large area, cyber criminals are constantly searching for vulnerabilities. Simius helps you to detect those vulnerabilities through the scans and security tests we offer. But there are plenty of ways that the bad guys will gather information on your network, for free.
There are hacking tools available which allow anyone to ride a bike and wardrive through entire neighborhoods. All of the information is consolidated and even centralized. That means the bad guys are going to hide their tracks without revealing what they’ve done.
Wardriving offers a cyber criminals with an easy attack vector. Multiple issues are associated with these types of attacks. So it is important for individuals to be aware of the risk. Oftentimes, threats become persistent. But it is the responsibility of smart home owners to secure their networks.

Never Use WEP – Please And Thank You
WEP or Wired Equivalent Privacy, is outdated. Do not use it. This is like giving hackers the keys to the kingdom, whenever they are within range. They will passively scan your network and see vulnerabilities. It also reveals security loopholes in your router security. So anyone is able to lookup your wardriving data, and see those vulnerabilities, then exploit them. Think of it like a hacker’s form of social media.
Not all wardriving is bad. There are open-source projects that are making this data available. This is yet another example of a double-edged sword. This data can be useful, but in the wrong hands it will reap havoc. Protecting a network against wardriving attacks is one thing, but guarding against persistent threats with access to that data is another. Simius employs common router and network exploits which are used by wardriving thugs. We will identify many of the common problems and breaches that the bad guys use to bypass your network.

Cyber Vigilance Ensures Your Safety
Most importantly, do not wait for a cyberattack to happen. Even though you might not think there is a risk, chances are good that someone is tapping into your personal location data. You won’t notice it, and there is plenty of opportunities for cyber criminals to attack. All while remaining incognito.
It is difficult for internet consumers to know about these risks. That is why Simius is seeking to educate our customer base with important information. At the same time, we simplify the problem in terms of common-sense.
Summary
In this article, we discussed wardriving and how it affects home network security. It is used by cyber criminals and security professionals, and presents risks as well as benefits. Just like any other piece of technology, treat it like a double-edged sword. We must use it wisely, but at the same time recognize the risks and be aware on how to defend against them. Simius will validate your network cyber defenses to ensure your home is protected against threats associated with wardriving.