When vulnerabilities are found, they are classified into categories or types. This makes it easier to identify possible solutions and simplifies the analysis of potential threats. Some vulnerabilities are based on code or programming errors, along with network or hardware design flaws. But others can be physical and based in the real world.

Types of Vulnerabilities
Cyber criminals only need one single vulnerability in order to access your systems. But multiple vulnerabilities can also be combined, to make matters worse. Luckily there is hope in discovery and prevention is critical.
Let us take a look at a full list of these vulnerability types. According to the International Standards Organization (ISO), the following list categorizes vulnerabilities based on the asset class they are related to.
- Hardware
- Susceptibility to humidity or dust
- Susceptibility to unprotected storage
- Age-based wear that causes failure
- Over-heating
- Software
- Insufficient testing
- Insecure coding
- Lack of audit trail
- Design flaw
- Network
- Unprotected communication lines
- Lack of cryptographic encryption
- Insecure network architecture
- Physical Site
- Area subject to natural disasters
- Interruption to power source
- Organizational
- Lack of regular audits
- Continuity plans
- Insufficient security
Problems with cyber security often seem invisible. However, it is evident that a pure technical approach cannot always protect physical assets. Case in point, social engineering attacks, such as a phishing scam can possibly lead to vulnerabilities being exposed. For example, an attacker could find a buffer overflow weakness. So they can exploit it and install malware, which is then used to exfiltrate sensitive data. In other words, the information being leaked could be absolutely anything. From bank accounts to smart camera video feeds, or even location data. Without identifying the risk, you won’t be able to have visibility to make a fix.

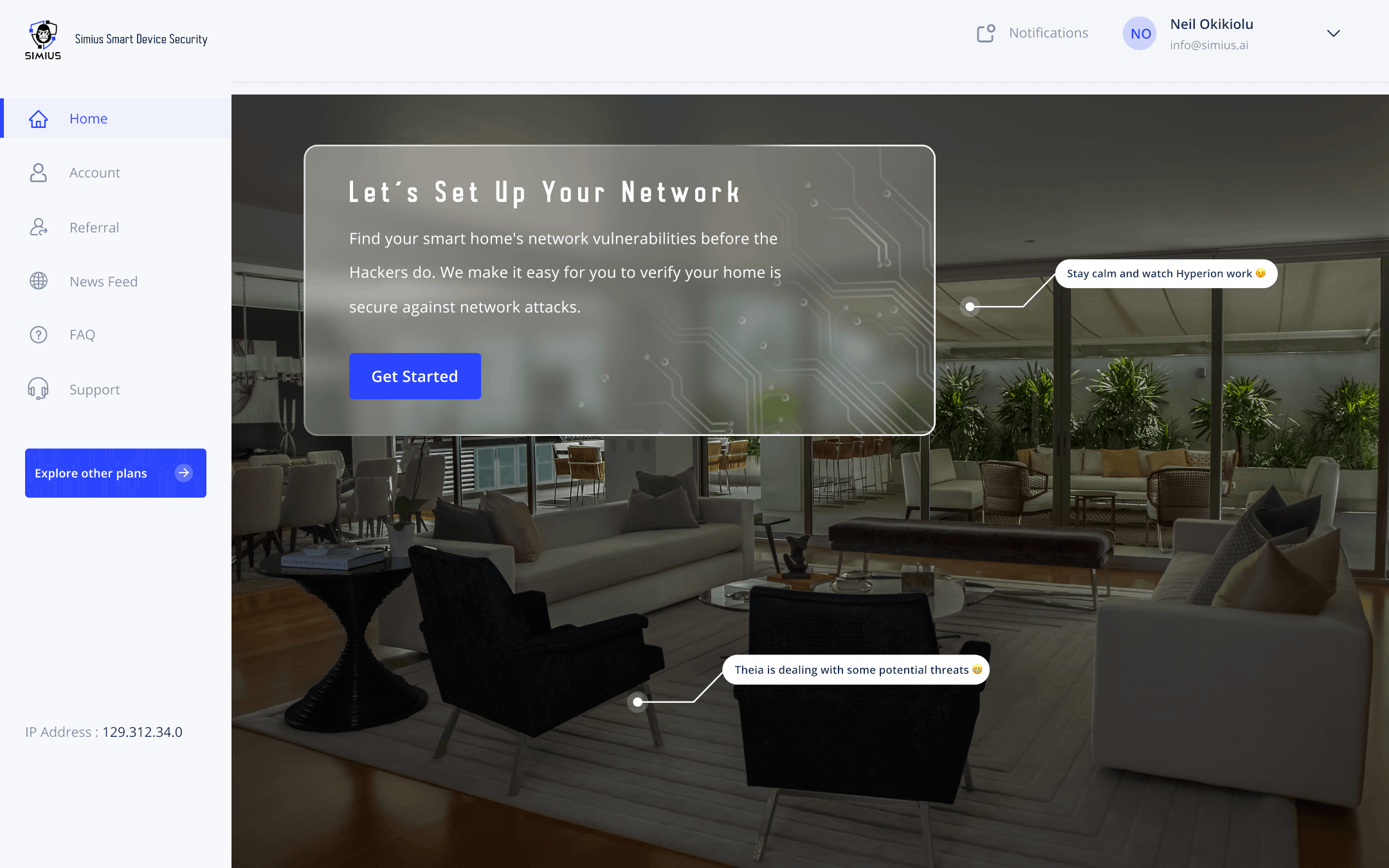
Scanning for Visibility
For all intents and purposes, we are wanting to give a higher-level view to the scope of these vulnerabilities. Simius helps to provide coverage over digital vulnerabilities which are less obvious. Namely, the software, hardware, and network-related issues. In addition, by carrying out your own vulnerability scans and knowing what type you are dealing with, Simius gives you the ability to take action on them.
Most importantly, the impact of a security breach can be very high and costly. Smart device owners are now facing increased risk, which they need to manage somehow. As mentioned in previously, it is very feasible to have that all done. This is the first step before using any other invasive methods to validate your smart devices and home network cyber security. Our services provide this with easy-to-use functionality. Using one-click features, as well as scanning placed on an automated schedule. Above all, this is intended to help you remain both aware and safe. After that, you take the time to concentrate on other things.
Knowledge is Power
Understanding that there are different types of vulnerabilities and knowing how to manage them, is no easy task. That is where Simius is offering premium services normally available to enterprises, exclusively. So having access to these tools is something that average smart device consumers are unable to use. With Simius, you have the option to scan your systems in the same way that large organizations operate their own security standards. But also keep in mind that there are some things which you need to consider which span outside the digital scope.

Physical vulnerabilities and care for the users of the technology should also be considered, which is why we advocate for strong cyber hygiene among our customers. Again, the first and best line of defense is you. So taking care of those basic things by your own awareness, and to all members of your household. Above all, it helps to minimize those risks.
Social engineering attacks can fool anyone these days. It is yet another confidence game, and the silver lining is found by bringing knowledge to the forefront. An ounce of prevention is worth a pound of cure, and knowing is always half the battle. We cannot place enough emphasis on those points, and our goal is to offer holistic solutions for these invisible problems. Therefore, always keep your smart devices secure both digitally and physically, as it will always require a multi-pronged approach.
Summary
In conclusion, we covered the types of vulnerabilities and how it relates to the scans offered by Simius. But there’s other vulnerabilities which are non-digital and we must entrust our users to maintain a high sense of cyber vigilance.