Table of contents
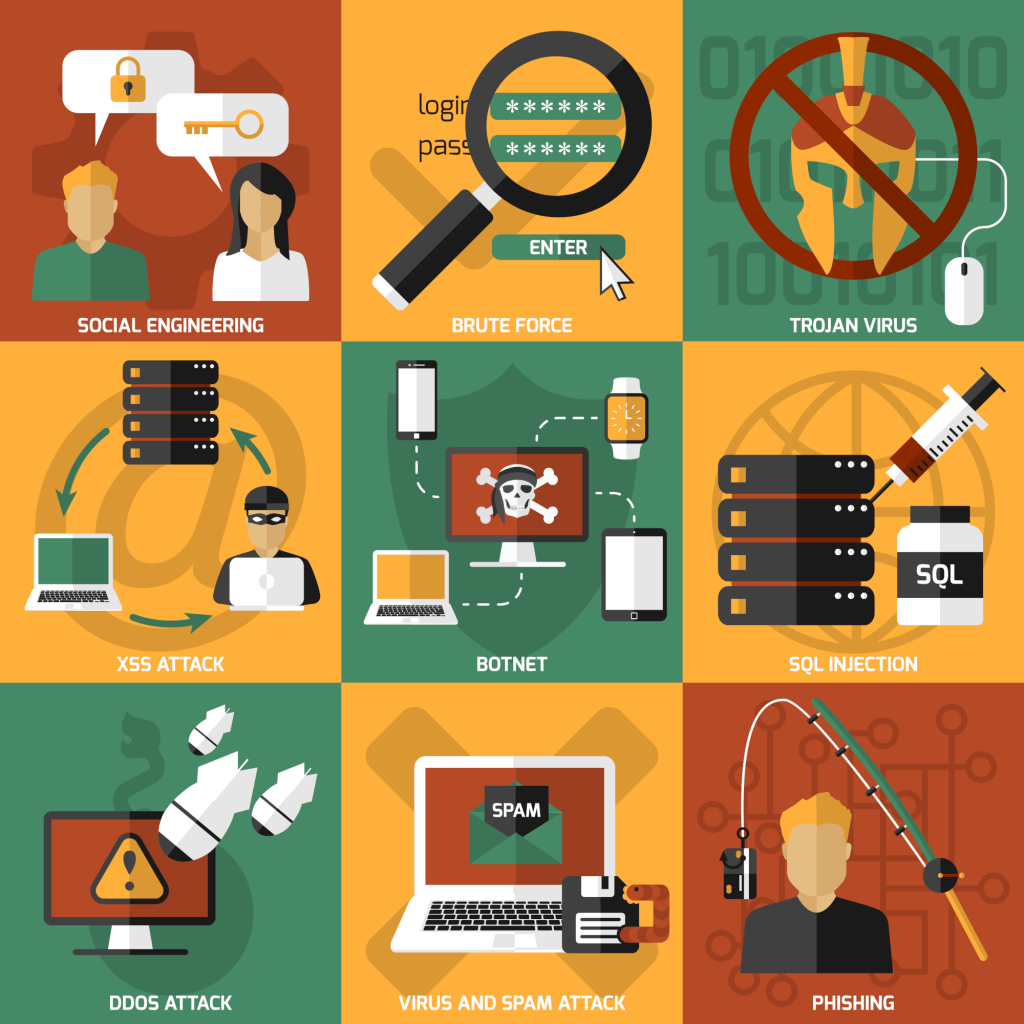
Facing a ransomware disaster is intimidating. But these cyber attacks are becoming all to common. It is difficult to understand what has happened. And most people do not have a plan on how to recover. At Simius, we want to inform our customers and provide tips for good cyber hygiene.
Prevention is Key
That is where a disaster recovery strategy comes in. Smart home owners need to be aware of industry standards, which are simple to adopt. The following list shows the essential steps which businesses must follow in case of ransomware attacks:
- Isolate and shutdown critical systems.
- Restore data from backups.
- Remediate, patch, and monitor.
- Enact a business continuity plan.
- Report the cyberattack.
Step 4 above isn’t applicable to the average smart home owner, per se. And in Step 2, we would also need to address any encrypted operating systems, since hackers can hold both data and computers or servers for ransom. The reason why is because there are complex installations or configurations which are difficult to build and implement. Imagine a sand castle versus an actual stone castle, a similar notion applies here. But we definitely prefer it being built out of stone or even steel. So, by having your own plan, even if its in the back of your mind, will go along way. This leads us to the notion of preparedness.

Have A Plan For Recovery
Since it is easy enough for us to work with some steps after the fact, please note that every action taken in advance will make recovery go smoother. Important considerations would be to first identify where your sensitive data is stored. Think images, videos, books, documents, files, and anything that would be difficult to recover if it was lost. If it cost money, or time, be sure you have a way of regenerating your digital assets. Include all of them in a backup of some kind. A ransomware disaster can affect any digital asset. If you have crypto, keep your savings on a USB that is not connected to the internet, and limit the time to a minimum when you need to connect online for buying or selling the currency.
There’s an old saying, which quickly overflowed into the world of computers. “Save, and Save Often.” That means if you are working on a large essay, or piece of writing, and any kind of work document, to click the Save button. Beyond anything financial, of course. Obviously, it ensures your work does not get lost. The same exact principle applies here. Autosave was introduced into video games for the exact same reason. One does not want to lose any progress, and the same should be true for smart home security.
Data Is The Number One Asset
If your family photos are not important enough to be saved on a backup device, then it makes them susceptible to ransomware. Otherwise, you could simply recover them if they become encrypted by cyber criminals who want to hold them ransom.
The same is true for any computer, smart phone, or even your connected IoT devices. Use the built-in services, including cloud backups whenever possible. This is extremely important for recovering from a ransomware disaster. But also, do not limit yourself to one backup. Having backup redundancy means you are keeping the same base covered from different angles. So, if a cloud backup fails to restore, you can go to a USB drive which was stored offline.
Each individual consumer must gauge and make the call for what backup methods to use. Keep them consistent, an capture snapshots at regular intervals. The longer time you wait between backups, the greater risk of losing anything in between.
Anticipate Any Losses
Some things may never be recovered, and you might be forced to live with it. In that case, you should also be prepared to accept and move on. There is no sense in dwelling over it, and instead look onward to the path ahead. Embrace the mistake as a lesson and learn how to never repeat it.
If critical systems are attacked however, be sure to have a direct backup plan and be capable of failover. For example, if your smart thermostat or refrigerator gets hacked. Be able to disconnect it and fail over onto manual processes for temperature control. Most of these systems should have that built-in, and if they don’t you should consider replacing them systems that do. At Simius, we are not in a position to advise on those specifics, but the main idea is not be entirely dependent on a smart device.
Seek Help
Also don’t be afraid to reach out for help. If you’ve had services for installing and maintaining smart devices, reach out to them immediately. They can help in those circumstances. With Simius, we allow you to test the security of those devices running on your network. It gives you the insight on any weaknesses, and is easily incorporated into smart home automation.
As such, Simius is designed to complement preparedness and it will have synergy with any disaster recovery strategy. By pre-emptively testing vulnerabilities, identifying loopholes in your smart home security, or in general removing those paths of entry, it will help prevent a ransomware disaster. This is how you change the game against the cyber criminals.
Summary
In this article, we discussed the basics of penetration testing and how it enhances network security. It is generally used among heavy industry and fortune 500 companies as part of their security auditing policies. It is proven to be effective at validating whether a vulnerability actually exists, and Simius is delivering that to our customers for their benefit.