In this post, we’re going to show you how easy it is for a hacker to compromise your smart home and why smart home network security is important.
Some Background
You may think that a hacker spends a lot of time looking for devices to compromise but that is not the case.
It is extremely easy for a hacker to scanned the Whole Internet (Over 3 billion devices in 1 hour) to search for vulnerable devices.
In fact hackers tend to have machines that routinely identify insecure devices and tag them for future attacks.
When talking about Embedded Devices (e.g. smart cameras, smart locks), all existing evidence shows that they are generally less secure than general purpose computers and are extremely easy to exploit.
In fact, at least 1 in 10 embedded devices are insecure (how many devices do you have at home?). It was also found that 96% of those insecure devices were still insecure after four months!
In the drivers seat
Here is the actual process of compromising your smart home network:
Reconnaissance: a hacker sets up a small physical computer or a computer in the cloud. This computer then automatically starts going through IP addresses (of which your smart devices have) and for every IP address it checks if there is an open port. Think of a port like a window in your home and an open port like an open window. Now, you can understand why a window left carelessly open can be very bad! The hacker’s machine identifies and stores information about each port left open (for the next step)
Identification: Now that the hacker has a list of open ports, they send messages to those ports and see how the device responds. The device’s response is used to detect what kind of device it is (e.g a baby monitor etc.)
Verification: Once the hacker has verified what device it is, the worst part begins! This is when the hacker begins to actually gain access to the device using easy to find tools. One thing to note is, this whole process is automated. The hacker can be sipping coffee while their computer accesses thousands of devices a second. Worst of all, you as a home owner will not even know it is happening.
Implications
Now that a hacker has access to your devices, they use that fact for many malicious purposes which can include:
- Accessing your smart home device feeds (e.g. a home camera feed)
- Accessing your data stored on other devices (don’t forget, once they have access through one device, the rest of your devices become vulnerable!)
- Using your devices to attack others and having links to the attacks traced back to your home (this is called a Botnet and is out of scope for our discussion)
- etc.
Conclusion
The future of smart home network security
With smart homes, we have been given this amazing technology. Unfortunately, most people not fully understand the dangers of mis-configuring said technologies or even the basics of smart home network security.
The dangers are even more magnified when a smart home owner realizes that hackers can now easily access the place where they sleep. The place where their children sleep, the place that is meant to be the safest for them.
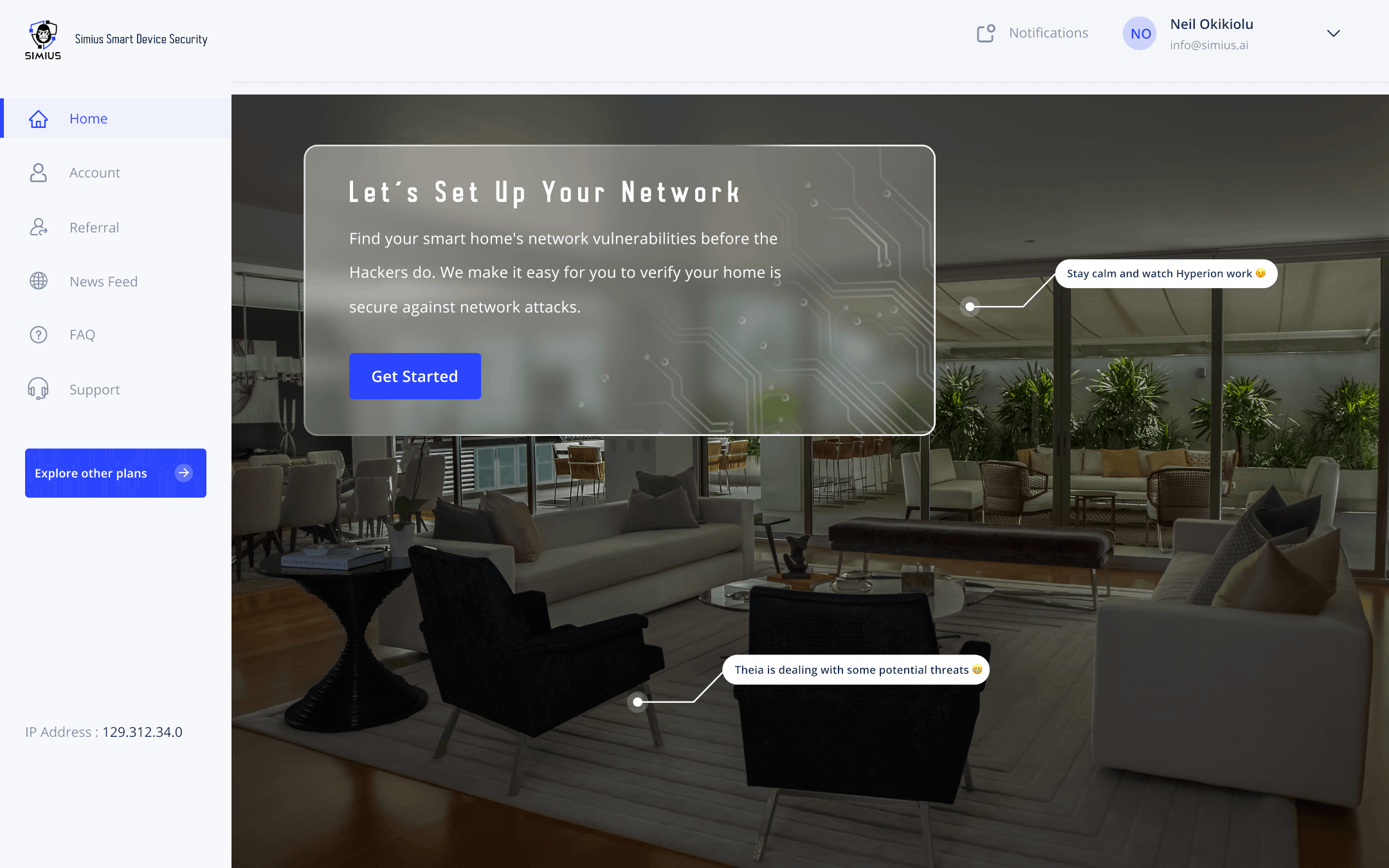
We hope you never have to experience the dangers written about here but as they say “Hope without action is just a Dream”. So act now! protect yourself and your family by Signing Up for Simius Smart Device Security
Sources
- Cui, Ang & Stolfo, Salvatore. (2010). A quantitative analysis of the insecurity of embedded network devices: Results of a wide-area scan. Proceedings – Annual Computer Security Applications Conference, ACSAC. 97-106. 10.1145/1920261.1920276.